下载evilginx
Go & Phish - Official Gophish integration released!
You can learn more about this update in the official blog post: https://breakdev.org/evilginx-3-3-go-phish/
CHANGELOG
Feature: Official GoPhish integration, using the fork: https://github.com/kgretzky/gophish
Feature: Added support to load custom TLS certificates from a public certificate file and a private key file stored in
~/.evilginx/crt/sites/<hostname>/. Will loadfullchain.pemandprivkey.pempair or a combination of a.pem/.crt(public certificate) and a.key(private key) file. Make sure to run without-developerflag and disable autocert retrieval withconfig autocert off.Feature: Added ability to inject
force_postPOST parameters into JSON content body (by @yudasm_).Feature: Added ability to disable automated TLS certificate retrieval from LetsEncrypt with
config autocert <on/off>.Feature: Evilginx will now properly recognize origin IP for requests coming from behind a reverse proxy (nginx/apache2/cloudflare/azure).
Fixed: Infinite redirection loop if the lure URL path was the same as the login path defined in the phishlet.
Fixed: Added support for exported cookies with names prefixed with
__Host-and__Secure-.Fixed: Global
unauth_urlcan now be set to an empty string to have the server return403on unauthorized requests.Fixed: Unauthorized redirects and blacklisting would be ignored for
proxy_hostswithsession: false(default) making it easy to detect evilginx by external scanners.Fixed: IP address
127.0.0.1is now ignored from being added to the IP blacklist.Fixed: Added support for more TLDs to use with phishing domains (e.g.
xyz,art,tech,wiki,lol& more)Fixed: Credentials will now be captured also from intercepted requests.
运行evilginx
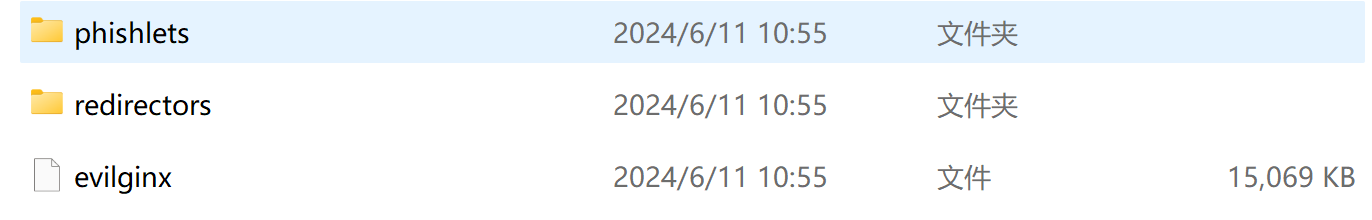
将下载evilginx 3..3版本程序及Phishlets页面上传服务器
运行命令evilginx
./evilginx配置域名解析
注意:启动前请将需要伪造的域名进行泛域名解析,如果未解析,将无法获取TLS证书。
配置DNS泛解析的步骤:
登录到你的DNS服务提供商的控制台。
找到你的域名管理页面,并进入DNS设置。
为指定的(子)域名添加一条新的A或NS记录:
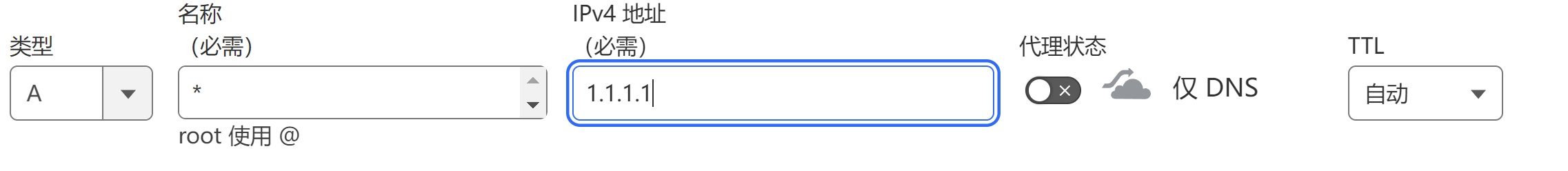
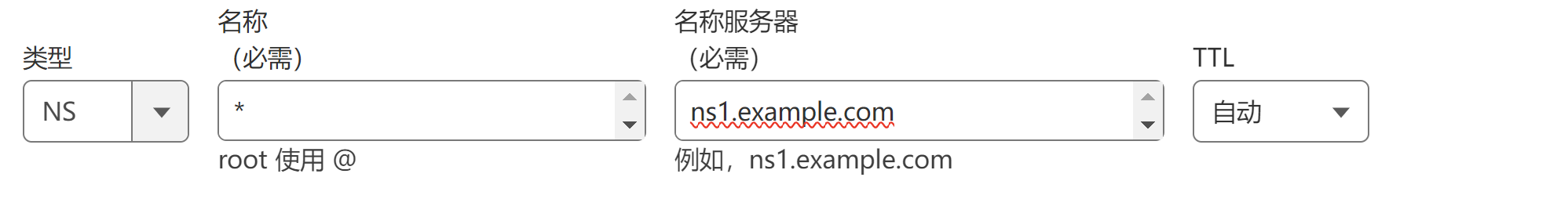
例如,在Cloudflare的DNS设置中,这可能看起来像这样:
类型:A
名称:*
IPv4地址:123.123.123.123
类型:NS
名称:*
名称服务器:ns1.example.com
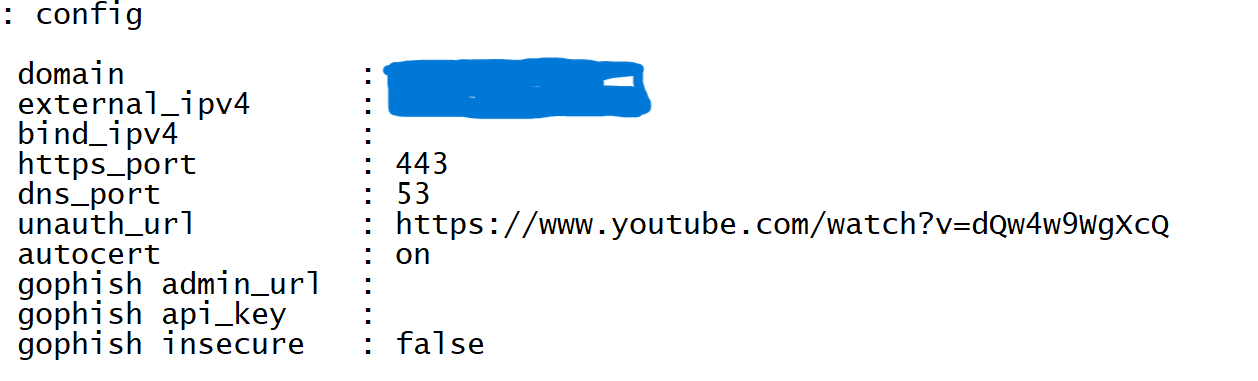
evilginx 配置
域名及公网IP
因为发布时需要使用SSL 证书,需要为evilginx 配置服务器公网IP及域名
config ipv4 external [ip]
config domain [domain][ip] 服务器外部或公网IP地址
[domain] 上方解析的域名,用于钓鱼时发布
配置phishlets
通过命令phishlets查看当前存在的phishlet
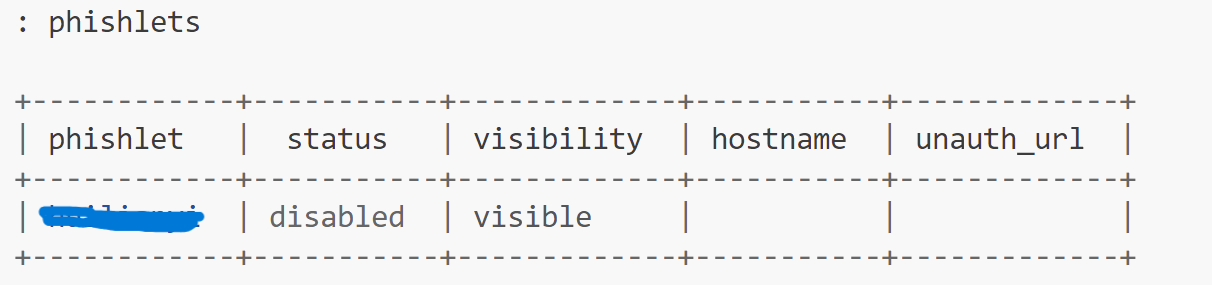
为phishlet 配置域名
phishlets hostname [phishlet] [domain][phishlet] 从以配置的模板选择一个
[domain] 定义一个域名,必须属于上方配置的子域名
启动模板
phishlets enable [phishlet]配置Lure
配置一个lure,默认从0开始生成一个ID号
lures create [phishlet]]获取钓鱼链接
lures get-url [ID]参考和声明
https://github.com/kgretzky/evilginx2